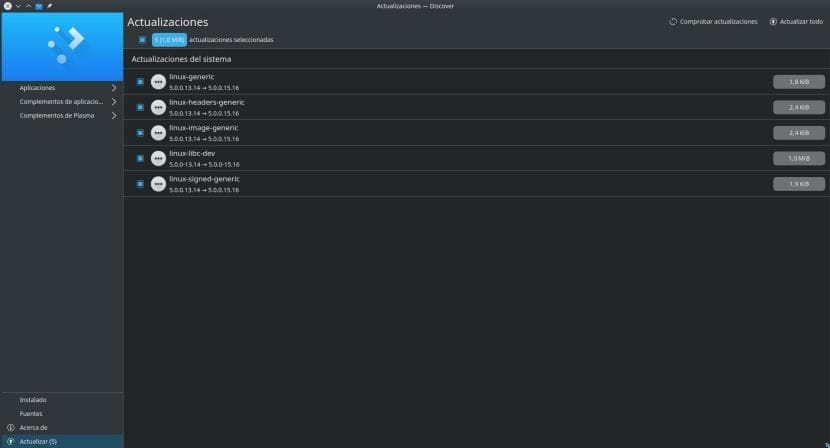
Recently, I discovered it a few hours ago, several vulnerabilities have been discovered that affect Intel processors from 2011 to today. These failures are known as Microarchitectural Data Sampling (MDS) and Canonical has already released new kernel versions for Ubuntu and the rest of its official flavors, which we remember are Kubuntu, Lubuntu, Xubuntu, Ubuntu Budgie, Ubuntu Mate, Ubuntu Studio and Ubuntu Kylin. The new versions arrive with the numbering 5.0.0.15.16, as long as we are in Disco Dingo.
As we read in its informative note, a total of four security flaws for which Intel has already released its firmware microcode to tackle the problem, but these firmwares could not be applied to Linux operating systems, so it is the companies that develop the systems who have to release new versions of their kernel and patches QEMU. It is worth remembering that this is a perfect occasion to try the Live Patch option that came with Disco Dingo, which allows us to install new versions of the Kernel without having to restart the system.
Canonical fixes 4 MDS security flaws
All four bugs affect multiple Intel processors and could allow (may if we don't upgrade) a malicious user exposing sensitive information. The problem affects all X-Buntu versions, among which are still supported 19.04, 18.10, 18.04, 16.04 and 14.04, the latter in the ESM version. It is also a perfect occasion to verify that the ESM support that is added to the 5 calendar years works.
As always when security updates are released, Canonical us recommends updating as soon as possible. On the other hand, it also recommends disabling SMT (Symmetric Multi-Threading or Hyper-Threading) from the BIOS, something that will be different depending on the computer and its BIOS version.
Although we have previously mentioned that Live Patch prevents us from having to restart when installing new versions of the Kernel, this time it can help us to verify that no message appears asking us to restart, but Canonical recommends restarting the computer due to the severity of the security flaws discovered. The new version of intel-microcode is 3.20190514.0. What is different is the kernel version, and the previously mentioned Disco Dingo version is added 4.18.0.20.21 for Ubuntu 18.10, 4.15.0-50.54 for Ubuntu 18.04 LTS and 4.4.0-148.174 for Ubuntu 16.04 LTS and 14.04 ESM. You know: update now, for what may happen.
